Research Project
The appchk research project is an effort to shine a light on the background activity of iOS apps, making the otherwise hidden network connections visible to everyone. The goal is to make privacy more accessible to the general public. And thus create incentives for app developers to respect users’ privacy.
We want to offer users, activists, data protection authorities, and data protection officers an easily accessible and flexible tool to assess the privacy measures of iOS applications.
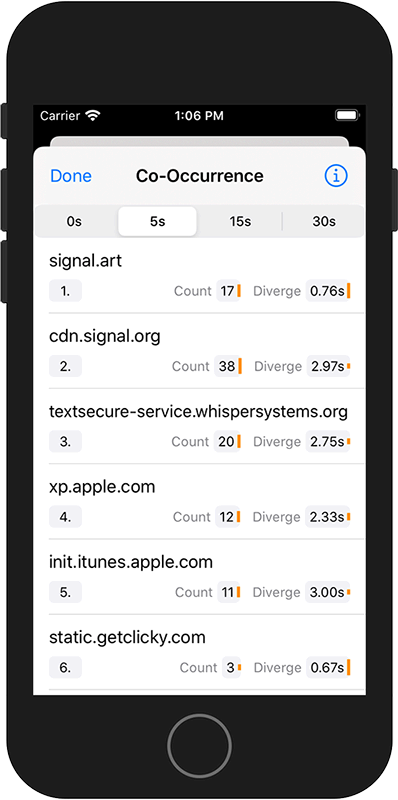
appchk allows users to:- get a visual overview of an apps communication signature
- assess how an app ranks within its peer group or category
- influence the ranking according to their preferences
Results
This website is the front-end of the evaluated data. All app recordings are collected and displayed here. Visually, it shows you how many known trackers an app uses. How apps compare to each other, and if there are privacy-friendly alternatives.
You can go to all apps directly. Or, if you’re interested in details, check the results section.
appchk – The App
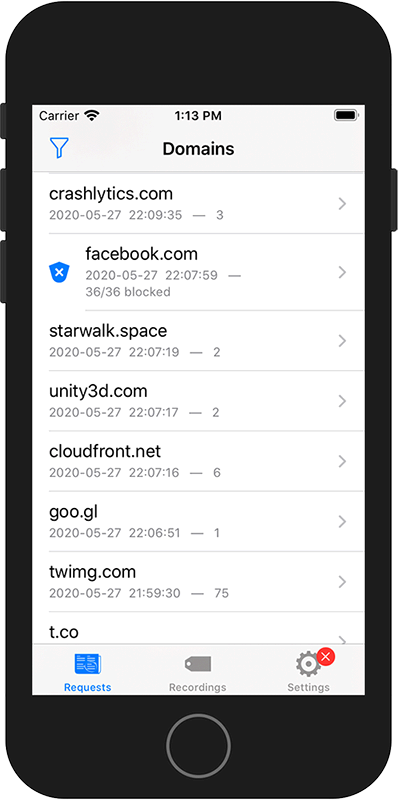
appchk is a pocket DNS monitor and network filter.
It helps you identify applications that communicate with other parties.
How does it work?
appchk creates a local VPN proxy to intercept all network connections. For each connection, appchk looks into the DNS headers only, namely the domain names. These domain names are logged in the background while the VPN is running. appchk does not need to be active all the time.
What about privacy?
Your data belongs to you. Therefore, monitoring takes place on your device only. appchk learns only the destination addresses, not the actual data that is exchanged. The app does not share any data with us or any other third-party – unless you choose to.
How can I contribute?
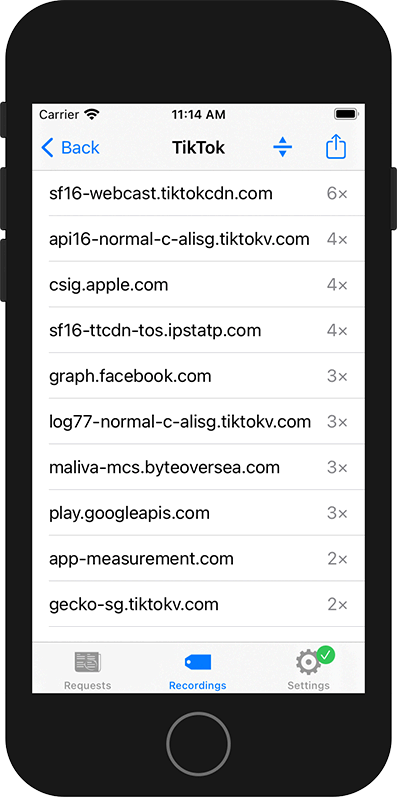
appchk allows you to record app-specific activity. You can share these recordings with the community; it can help you and others avoid phony applications, even before you install an app.
Get the iOS App and contribute.
Join the TestFlight Beta.
Source code is available on GitHub.
Limitations
Due to the network extension’s technical limitations, appchk can not detect if a network activity belongs to one app or another. It may result in wrong attributions. The attributions can be minimized by running only a single application during recording and filter results before contributing. The evaluation website will ignore requests that appear only in a small subset of recordings.
This project is limited to iOS applications. But there are similar projects for Android apps and websites. Check these out:
> TrackerControl is an Android application that detects and prevents in-app tracking. It uses the same approach as appchk does. Analyzing DNS traffic on device with a local VPN extension.
> PrivacyScore.org is a tool to analyze websites. It allows you to create lists for comparison and ranking. Not only does it show you how much tracking is present in a given website. It also gives you a report on technical security and privacy measures. This way you can evaluate related websites and choose the one with greater privacy benefits.